Quantum-safe security is becoming a practical business topic, not a distant laboratory concern. The most urgent issue is not that a quantum computer will break every encrypted connection tomorrow. The real risk is “harvest now, decrypt later”: attackers collect sensitive encrypted data today and wait until stronger quantum systems can decode it.
For Muawia Tech readers, this matters because long-lived data is everywhere: customer records, contracts, identity documents, backups, source-code archives, health records, financial files, and internal strategy documents. If that information must remain private for years, organizations should start preparing for post-quantum cryptography before the migration becomes rushed and expensive.
Why Quantum-Safe Security Is Trending Now
Recent security and infrastructure announcements show that vendors are moving quantum readiness into mainstream platforms. Fortinet’s FortiOS 8.0 messaging, for example, combines AI-driven security, SASE, and quantum-safe capabilities. Investor coverage of quantum startups is also shifting from “wait for perfect machines” to near-term software, integration, and security readiness. Together, these signals show that quantum planning is moving from research roadmaps into enterprise risk management.
The timing is important. Cryptographic migrations are slow. Businesses have to inventory certificates, VPNs, APIs, mobile apps, embedded devices, identity providers, backup systems, and third-party integrations. Even if the most powerful quantum threat is still years away, the preparation window is now.
What “Harvest Now, Decrypt Later” Means
In a harvest-now-decrypt-later scenario, an attacker copies encrypted traffic or encrypted files without needing to read them immediately. The data is stored until future technology makes decryption easier. This is especially dangerous for information with a long confidentiality lifetime. A password reset token may expire quickly, but legal agreements, government identifiers, intellectual property, and medical data can remain sensitive for decades.
Traditional security programs often focus on present-day compromise: phishing, ransomware, cloud misconfiguration, and malware. Quantum-safe planning adds another lens: how long must this data remain secret, and which cryptographic systems protect it?
Who Should Care First?
Organizations with long-lived confidential data
Banks, clinics, legal firms, universities, government suppliers, insurers, and technology companies should be early planners. If encrypted records would still be valuable in five, ten, or twenty years, the risk deserves board-level attention.
Teams running public-key infrastructure
Public-key cryptography is deeply embedded in TLS, VPNs, device identity, code signing, document signing, and enterprise authentication. A company that does not know where certificates and keys live will struggle to migrate safely.
Cloud and SaaS-heavy businesses
Modern businesses rely on many cloud services. Quantum-safe security therefore requires vendor questions: Which cryptographic algorithms are used? What is the migration roadmap? Are hybrid post-quantum options available? How will certificates be rotated?
A Practical Quantum-Safe Security Roadmap
1. Create a cryptography inventory
List where encryption, signing, and key exchange are used. Include web servers, VPNs, email security, device management, APIs, databases, backups, mobile applications, CI/CD pipelines, and third-party services. The inventory does not need to be perfect on day one, but it must be owned and updated.
2. Classify data by confidentiality lifetime
Not all data needs the same protection. Sort data into categories: short-term, medium-term, and long-term confidentiality. Long-term data should receive the earliest quantum-readiness attention because it is the most attractive target for harvesting.
3. Track standards and vendor roadmaps
Security teams should follow post-quantum cryptography guidance from standards bodies and major platform vendors. Ask vendors whether they support hybrid modes, certificate agility, automated rotation, and clear migration timelines. Avoid custom cryptography unless you have specialist expertise.
4. Test crypto agility
Crypto agility means the ability to change algorithms, keys, certificates, and libraries without rewriting every system. Test whether your applications can rotate certificates quickly, update TLS settings, and replace cryptographic libraries. If rotation is painful today, a post-quantum migration will be harder tomorrow.
5. Prioritize exposed and high-value systems
Start with internet-facing services, remote-access systems, code-signing infrastructure, high-value APIs, and repositories containing sensitive intellectual property. These systems are easier for attackers to observe or target and often protect data with long-term value.
Common Mistakes to Avoid
- Waiting until a crisis forces a rushed migration.
- Assuming cloud providers handle every cryptographic dependency automatically.
- Ignoring old backups, archives, and embedded devices.
- Buying “quantum security” products without a clear inventory or risk model.
- Focusing only on algorithms while forgetting key management and certificate rotation.
How Small Businesses Can Start
Small businesses do not need a full cryptography lab. Start with basic governance. Identify the systems that store customer data, financial records, passwords, contracts, and business-critical backups. Confirm that websites and cloud services use modern TLS. Ask critical vendors about their post-quantum roadmap. Keep systems patched and remove obsolete encryption protocols.
For many teams, the first win is visibility. If you know which systems protect long-lived data, you can make better decisions when vendors release quantum-safe updates.
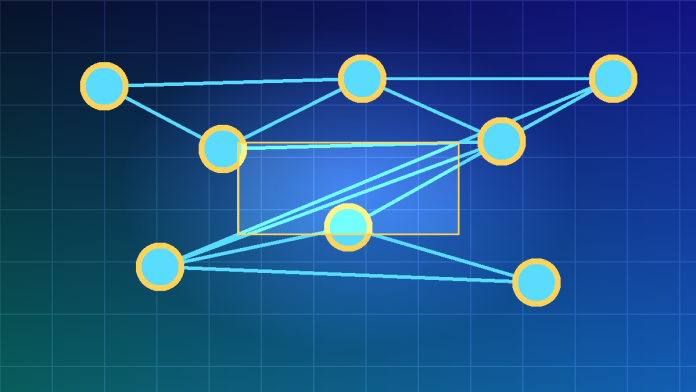
Connection to AI, Cloud, and Modern Security
Quantum-safe planning overlaps with current cloud and AI security work. AI systems increase the amount of data being processed and moved between tools. Cloud services create complex dependency chains. Security platforms are adding automation to keep up with faster attacks. In this environment, cryptographic resilience becomes another layer of operational maturity.
Businesses that already practice strong identity management, asset inventory, backup protection, and vendor risk review will find quantum readiness easier. The same discipline applies: know what you own, know who can access it, and know how to replace weak controls before attackers exploit them.
FAQ
What is quantum-safe security?
Quantum-safe security is the practice of preparing systems, data, and cryptography for a future where quantum computers may weaken some current public-key algorithms.
Is quantum computing already breaking encryption?
No mainstream evidence shows general internet encryption being broken at scale by quantum computers today. The near-term concern is long-term data exposure and slow migration timelines.
What is harvest now, decrypt later?
It is an attack strategy where adversaries collect encrypted data now and store it until future capabilities allow them to decrypt it.
Should businesses replace all encryption immediately?
No. Businesses should inventory cryptography, classify long-lived data, follow standards-based guidance, and migrate in a planned way as mature options become available.
Questions for Vendors and Internal Teams
Before buying a new platform or renewing a critical service, ask direct questions. Does the vendor maintain a cryptographic bill of materials? Which TLS libraries, certificate authorities, and signing systems are in use? Is there a documented post-quantum plan? Can customers test hybrid certificates or quantum-safe key exchange in a staging environment? How will the vendor communicate breaking changes?
Internal teams should answer similar questions. Who owns certificate lifecycle management? Are old protocols still enabled for compatibility? Are backups encrypted with keys that can be rotated? Are secrets stored in a central vault? Are code-signing keys protected with hardware-backed controls? These operational details matter as much as the algorithm names. Documenting the answers now also helps auditors, insurers, partners, and customers see that quantum risk is being managed as a normal resilience program rather than a last-minute emergency project.
Conclusion
Quantum-safe security is about preparation, not panic. The smartest move in 2026 is to build a clear inventory, understand which data must stay private for years, demand vendor roadmaps, and improve crypto agility. Companies that begin now will avoid rushed decisions later and will protect customer trust as the next era of computing arrives.